Secret Management: What Every Product Manager Needs to Know in Cybersecurity
- Aug 15, 2025
- 3 min read
As a product manager overseeing AI-driven products, you’re responsible not just for shipping features, but for defending your users, data, and business from real-world cybersecurity threats. The invisible—but critical—element in this equation? How your team handles API keys, tokens, and database credentials.
Why It Matters for Product Managers
Think:
Unauthorized access and data breaches
Financial fraud if payment APIs are exposed
Service disruption from attackers meddling with your systems
Intellectual property theft of proprietary algorithms or datasets
Unfortunately, too many teams still hardcode credentials into scripts, config files, or environment variables and call it a day. This is the security equivalent of leaving your house keys under the doormat.
It’s easy to think of sensitive credentials as “just a dev problem.” But when secrets leak, the fallout lands squarely on your roadmap and reputation:
Customer trust: Data breaches or unauthorized access instantly erode user confidence—which can be incredibly hard (and expensive) to rebuild.
Compliance headaches: Exposed credentials can mean failed audits, legal trouble, and costly remediation.
Downtime and disruption: Attacks on your agents can halt critical services, creating support floods and revenue risks.
Unplanned engineering work: Recovering from leaked secrets usually means urgent fire drills, distracting development from growth initiatives.
A Product Manager’s Framework: Why Secret Management Powers Product Delivery
Here’s what Product Manager should focus on to assure cybersecurity safety:
Security by Design: Centralizing secrets and enforcing role-based access ensures your product team doesn't accidentally expose sensitive data—reducing risk early in the development lifecycle.
Agility for Launches: Automated rotations and dynamic credential delivery mean you don’t have to coordinate manual “key swaps” for every deployment. This keeps launches fast and smooth.
Resilience and Recovery: With auditing and monitoring in place, your incident response playbook gets a huge upgrade—quickly spotting (and stopping) suspicious activity before it turns critical.
Scalability for Growth: Secure management becomes frictionless for onboarding new engineers, expanding features, or integrating third-party APIs as your product grows.
Why I Like Locker Secret Manager Specifically
End-to-End & Zero-Knowledge Encryption — even CyStack can’t read your secrets.
Open Source — anyone can audit the code for trust and transparency.
Automatic Rotation — reduces the risk of stale credentials.
Secrets Detector — scans your codebase for exposed keys during migration.
Role-Based Access Control — perfect for teams collaborating on AI systems.
Cloud & Self‑Hosted Options — match your infrastructure and compliance needs.
For technical guys, here’s your double click on Locker Secret Manager technology:
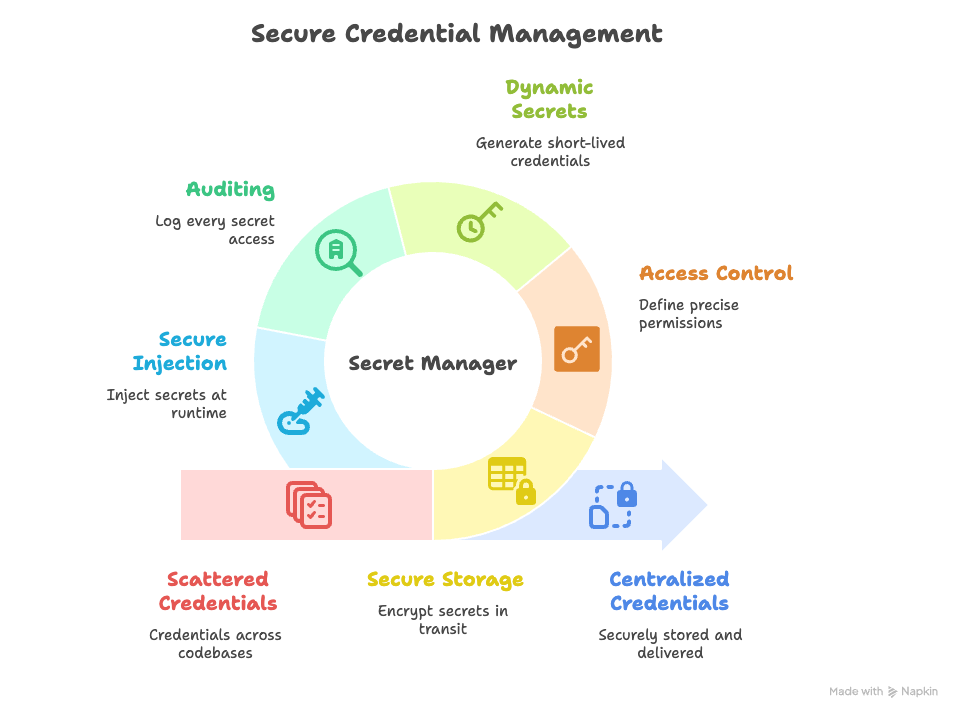
Instead of scattering credentials across codebases and deployments, a secret manager stores and delivers them securely, only when and where they’re needed. Here’s how:
1. Centralized, Secure Storage
Encrypt secrets in transit and at rest (AES-256, zero‑knowledge).
No more API keys in GitHub repos or .env files.
Even if the storage location is breached, secrets remain unreadable.
2. Access Control & Least Privilege
Define precise permissions for each AI agent or service.
Integrate with IAM so only approved entities can request secrets.
Agents only get access to what they absolutely need.
3. Dynamic Secrets & Rotation
Generate short-lived credentials just-in-time.
Automate rotation so leaked keys quickly become useless.
4. Auditing & Monitoring
Every secret access is logged.
Detect unusual patterns — like an agent requesting secrets it shouldn't.
5. Secure Injection at Runtime
Inject secrets directly into the agent’s environment at runtime.
Developers never even see the keys.
The Takeaway for Product Managers:
If secret management isn’t part of your roadmap discussions, you’re leaving your product exposed. Secure, automated secrets handling is a foundational platform decision—not just a security upgrade. Championing it protects your users, future-proofs your product, and keeps your team focused where they belong: building great experiences, not fighting fires.
API keys, database passwords, authentication tokens — all of these are the lifeblood of your AI agent’s ability to interact with the outside world. And here’s the uncomfortable truth: if those secrets leak, the damage can be catastrophic.


